The term “device fingerprinting” doesn’t sound like something most people notice, but it quietly powers how modern platforms recognize and track users. Every time a browser loads a page, it reveals small details settings, configurations, and behaviors that seem harmless on their own. But when combined, those details form a unique pattern, one that can identify a device without ever asking who the user is.
Disclaimer: This article is for educational, documentary, and research purposes only. It does not promote, facilitate, or encourage any form of illicit activity. All terminology, systems, and narratives are described strictly for cultural, cybersecurity, and historical analysis.
I. Introduction: When the Browser Became an Identity
Device fingerprinting rarely appears in everyday conversation, yet it sits quietly behind how modern systems recognize users. Long before people began questioning online anonymity, browsers were already exposing small pieces of information, details so minor they seemed irrelevant. But over time, those details began to form patterns.
And patterns, when analyzed at scale, become identity.
This shift didn’t happen overnight. It evolved gradually, as platforms moved from relying on what users provided to what systems could observe. What once felt like anonymous browsing slowly transformed into a space where identity could be reconstructed without direct input.
II. Understanding Device Fingerprinting
At its core, device fingerprinting is about recognition without explicit identifiers. Instead of asking who are you?” Systems ask, “What does your device reveal?”
Every browser exposes a set of characteristics:
- Version and type
- Operating system
- Screen size and resolution
- Installed fonts
- Language and timezone
Individually, these signals are common. But when combined, they create a configuration that can often be distinguished from millions of others.
It is this combination—not any single element—that defines a fingerprint.
III. The Shift From Cookies to Observation
In the early days of the web, tracking relied heavily on cookies. These small files stored data on a user’s device, allowing websites to recognize returning visitors.
But cookies had limits.
They could be deleted. They were tied to specific domains. And they required storage.
Fingerprinting approached the problem differently. Instead of storing identifiers, it observed existing ones. Instead of relying on persistence, it relied on reconstruction.
This marked a major transition—from stored identity to inferred identity.
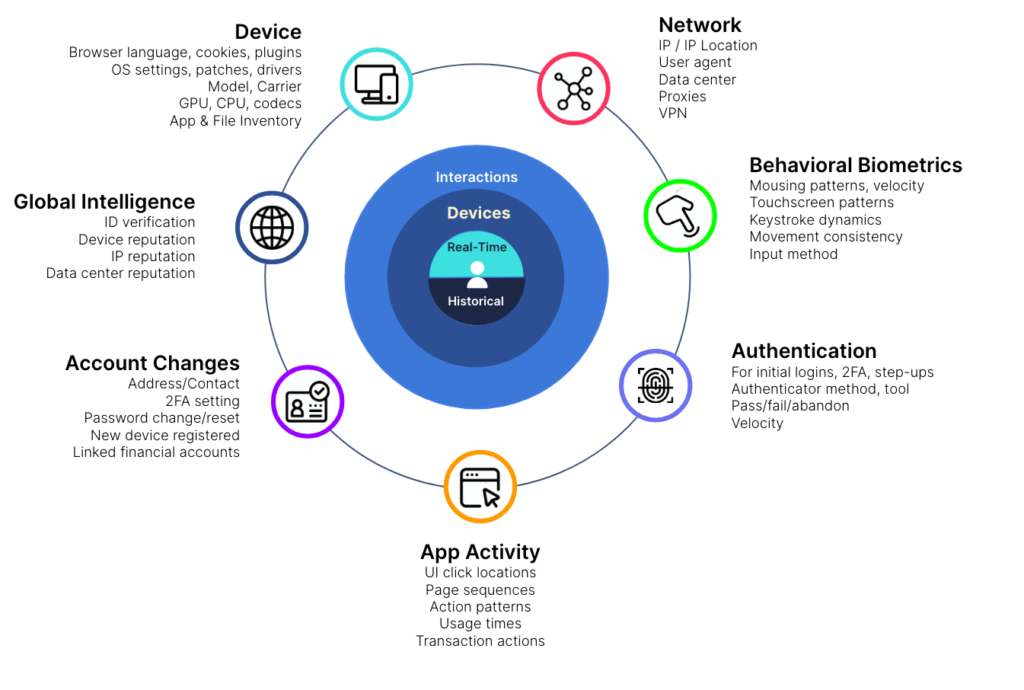
IV. The Expansion Into Behavioral Patterns
As systems evolved, fingerprinting moved beyond static data.
Behavior became part of the equation.
- How quickly someone types
- How a cursor moves across the screen
- How long it takes to interact with elements
These signals added depth. Identity was no longer tied only to a device but to interaction patterns.
This shift reflects a broader trend: systems becoming less dependent on fixed data and more reliant on dynamic behavior.
V. Device Fingerprinting in Modern Systems
Today, device fingerprinting operates across multiple layers of the internet.
It contributes to:
- Security systems
- Risk analysis
- Platform optimization
It rarely appears directly to users, yet it influences outcomes in subtle ways.
As discussed in our analysis of DNS and OPSEC, infrastructure already reveals patterns at a network level. Fingerprinting adds another dimension—one that focuses on the user rather than the system.
VI. Persistence Without Storage
One of the defining characteristics of fingerprinting is persistence.
Unlike cookies, which can be cleared, fingerprints are recreated each time a device interacts with a system. This makes them resilient to simple changes.
It also changes how persistence is understood.
Instead of storing identity, systems rebuild it.
VII. Interaction With Broader Data Systems
Fingerprinting does not exist in isolation. It works alongside other forms of data collection.
These include:
- Network-level signals (IP data)
- Infrastructure mapping (DNS relationships)
- Historical tracking (passive DNS records)
As explored in passive DNS and digital footprints, these layers combine to create a timeline of activity.
Fingerprinting adds depth to that timeline, connecting actions to devices and patterns.
VIII. The Decline of Traditional Anonymity Models
Earlier models of anonymity relied on limited identifiers. Changing one element could significantly alter how a system perceived a user.
Modern systems operate differently.
They evaluate multiple signals at once, reducing reliance on any single point of identification.
This makes anonymity less about removing data and more about understanding how systems interpret patterns.
IX. The Illusion of Simplicity
There is often a gap between what users believe and how systems actually function.
Actions that feel significant may have limited impact when viewed within a broader analytical framework.
This creates an illusion of control where changes appear meaningful but do not fully alter underlying patterns.
X. Cultural Awareness and Shift in Perspective
As awareness of tracking technologies increases, device fingerprinting has moved from a technical concept to a cultural one.
It represents a shift in how identity is understood:
- From explicit to inferred
- From static to dynamic
- From visible to invisible
This shift influences how people think about privacy, security, and presence online.
XI. Fingerprinting as Part of a Larger System
To fully understand device fingerprinting, it must be viewed as part of a larger system.
It connects with:
- Payment systems (as seen in non VBV BINs 2026 discussions of evolving verification)
- Infrastructure patterns (DNS relationships)
- Historical records (passive DNS data)
Together, these layers form a multi-dimensional view of activity.
XII. Why This Matters Today
Device fingerprinting is not just a technical concept; it reflects a broader transformation in how systems operate.
It shows how:
- Data is interpreted rather than collected
- Identity is constructed rather than declared
- Systems rely on patterns rather than single identifiers
Understanding this shift is key to understanding the modern internet.
XIII. Conclusion: Identity Without Visibility
The idea of anonymity has changed.
It is no longer defined solely by what is hidden but by what can be inferred.
Device fingerprinting illustrates this shift clearly. It shows how identity can emerge from patterns, even when no direct information is provided.
In this environment, the concept of being unrecognized becomes more complex.
Not because systems know everything—but because they can connect enough details to form a picture.
And that picture, once formed, becomes difficult to ignore.
XIV. Frequently Asked Questions (FAQ)
What is device fingerprinting?
A method of identifying devices based on observable characteristics rather than stored identifiers.
How is it different from cookies?
Cookies store data, while fingerprinting reconstructs identity from existing signals.
Why is it important?
It plays a role in security, analytics, and understanding system behavior.
Is it used alone?
No, it works alongside other data systems to build a broader view of activity.