In 2026, searches for “DNS and OPSEC” have grown alongside a broader interest in how hidden infrastructure shapes the internet’s most complex ecosystems. What was once dismissed as background configuration is now recognized as a critical layer in understanding visibility, traceability, and long-term exposure.
Disclaimer: This article is for educational, documentary, and research purposes only. It does not promote, facilitate, or encourage any form of illicit activity. All terminology, systems, and narratives are described strictly for cultural, cybersecurity, and historical analysis.
I. Introduction: The Infrastructure Nobody Saw
Long before cybersecurity became a mainstream concern, the internet operated on a fragile balance of trust, speed, and assumption. In underground circles between 2010 and 2016, attention was rarely directed toward infrastructure. Conversations revolved around marketplaces, tools, vendors, and so-called “methods,” while the systems that made everything visible the invisible wiring of the web—remained largely unexamined.
At the center of that invisible layer was the Domain Name System (DNS). To most users, DNS was a silent translator, converting names into addresses. To operators building digital ecosystems forums, storefronts, mirrors, or marketplaces it was a setup detail, not a strategic decision.
By 2026, that perception has shifted dramatically. DNS is no longer a background process; it is one of the most revealing components of digital infrastructure. What once served as a neutral mapping system has become a historical ledger one capable of exposing relationships, patterns, and structural weaknesses across entire networks.
II. DNS as Infrastructure: More Than a Phonebook
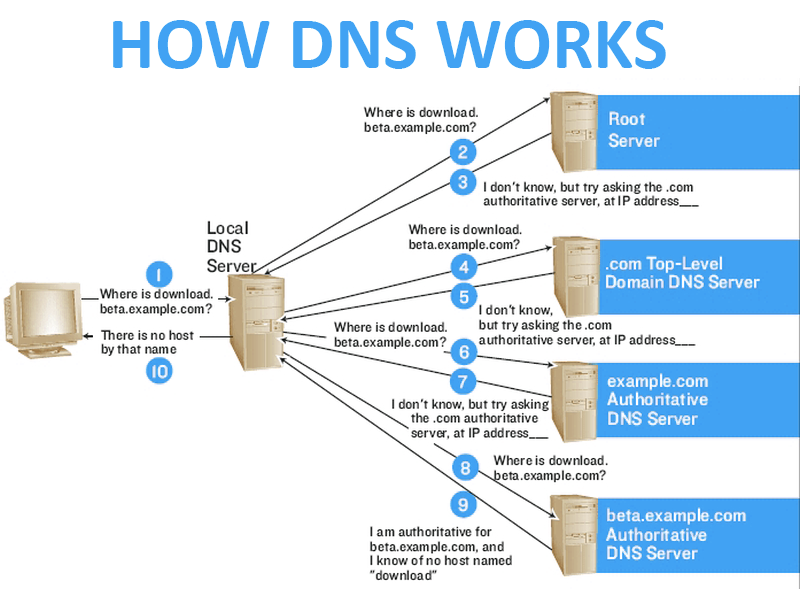
The common explanation of DNS as a “phonebook of the internet” simplifies its role but obscures its significance. DNS is not just about translation—it is about visibility, control, and traceability.DNS and OPSEC
Every domain name carries with it a set of attributes that define its existence:
- Nameservers that point to authoritative sources
- Registrar data that ties it to a provider
- Historical resolution records linking it to IP addresses
- Timing patterns that reveal deployment and migration cycles
Together, these elements form an infrastructure fingerprint. While individual components may appear harmless, their aggregation creates a narrative a record of how a domain lives, moves, and interacts with the wider internet.
In underground ecosystems, where anonymity is often assumed rather than engineered, this narrative becomes particularly revealing.
III. The Early Underground Era (2010–2015): Speed Over Structure
The early 2010s represented a formative period for underground digital economies. Forums such as CrdPro, Altenen, and various invite-only boards served as hubs for information exchange. The focus was overwhelmingly tactical: where to buy, what to use, which platforms worked.
Infrastructure decisions were secondary. Domains were registered quickly, often through the same handful of providers. Nameservers were reused across multiple projects for convenience. Little thought was given to long-term exposure.
This resulted in what can be described as “flat infrastructure” systems that functioned effectively in the short term but lacked segmentation. A single operator might run multiple domains, all tied together through identical DNS configurations.
At the time, this did not appear problematic. The emphasis was on uptime, accessibility, and speed. The assumption was that if a domain was compromised, it could simply be replaced.
IV. Nameservers as Persistent Identifiers
While domains are transient, nameservers often persist. This distinction is critical.
A domain can be abandoned, replaced, or rebranded. Content can be wiped. Servers can be relocated. But nameserver configurations frequently remain consistent, especially when managed for convenience.
Over time, this created clusters of domains linked by shared infrastructure. What appeared as separate entities at the surface level were, at a deeper layer, connected through identical DNS configurations.
For analysts, this offered a powerful insight. Nameservers acted as a form of passive identifier—not explicitly revealing ownership, but suggesting relationships.
The pattern was simple but effective:DNS and OPSEC
- Identify a nameserver
- Map all domains associated with it
- Observe patterns of deployment and timing
Through this process, entire ecosystems could be reconstructed.

V. The Emergence of Passive DNS and Historical Memory
As cybersecurity capabilities evolved, so did the ability to collect and analyze DNS data. Passive DNS systems began to store large-scale resolution data, effectively creating a historical archive of domain behavior.
This marked a turning point.
DNS was no longer ephemeral. It became persistent.
Analysts could now:
- Track how domains changed over time
- Identify when infrastructure shifted
- Link seemingly unrelated domains through shared history
For underground ecosystems, this introduced a new challenge. Actions that were once considered temporary now left permanent traces.
The concept of “burning” a domain lost its effectiveness when its historical footprint remained accessible.
VI. OPSEC in Theory vs DNS and OPSEC in Practice
Operational security, often abbreviated as OPSEC, is frequently discussed in underground communities as a set of principles designed to preserve anonymity. In practice, however, OPSEC is shaped by human behavior.
The tension between security and convenience is constant.
Common convenience-driven behaviors included:
- Reusing familiar registrars
- Maintaining consistent nameserver configurations
- Centralizing control of multiple domains
These decisions reduced complexity but increased exposure. Over time, they created patterns that could be identified and analyzed.
OPSEC, in this context, was less about tools and more about discipline. The absence of that discipline resulted in infrastructure-level correlations that were difficult to conceal.
VII. Domain Churn and the Myth of Disappearance
One of the defining assumptions of early underground ecosystems was that domains were disposable. If a site became compromised or flagged, it could be replaced quickly with minimal consequence.DNS and OPSEC
This assumption proved incomplete.
While domains themselves could disappear, their associated data did not. DNS records, nameserver associations, and historical mappings remained accessible through various analytical tools.
This created a distinction between disappearance and persistence.
A domain might no longer resolve, but its historical presence continued to exist within the broader data ecosystem.
VIII. Fragmentation and Adaptation (2018–2026)
By the late 2010s, awareness of infrastructure-level exposure began to increase. Operators adapted by introducing fragmentation into their systems.
This included:
- Distributing domains across different nameservers
- Separating projects into isolated environments
- Increasing variability in infrastructure configurations
At the same time, defensive systems became more sophisticated. Registrars implemented stricter monitoring, and analytical tools became more accessible.
The result was an ongoing tension between visibility and obscurity. Each adaptation introduced new complexities while attempting to reduce exposure.
IX. DNS as a Cultural Artifact
Beyond its technical role, DNS also reflects the cultural evolution of underground ecosystems.
Patterns observed in DNS data often mirror broader trends:
- The rise and fall of marketplaces
- The migration from forums to encrypted messaging platforms
- The shift from centralized systems to fragmented networks
In this sense, DNS functions as both infrastructure and archive. It records not only technical relationships but also the lifecycle of digital communities.
X. The Weak Link That Became a Lens
Nameservers were never designed to serve as identifiers. Their purpose was purely functional—to direct traffic efficiently.
However, within the context of underground operations, they became something more. They evolved into a lens through which entire ecosystems could be examined.
This transformation highlights a broader theme in cybersecurity: systems designed for convenience can become points of exposure when analyzed at scale.
XI. Frequently Asked Questions (FAQ)
What is DNS in simple terms?
DNS is a system that translates domain names into IP addresses, allowing users to access websites without needing to remember numerical identifiers.
Why are nameservers important in infrastructure analysis?
Nameservers define where a domain’s DNS records are managed. Consistent use of nameservers across multiple domains can reveal structural relationships.
What is passive DNS?
Passive DNS refers to the collection and storage of historical DNS resolution data, allowing analysts to study how domains and IP relationships evolve over time.
Why is DNS considered a weak link in OPSEC?
Because DNS configurations often reveal patterns and relationships that persist over time, even when other elements of infrastructure change.
Is DNS still relevant in modern cybersecurity research?
Yes. DNS remains one of the most valuable sources of information for understanding network behavior, infrastructure design, and historical patterns.
X. Conclusion: DNS and OPSEC in a Persistent Internet
By 2026, the relationship between DNS and OPSEC is no longer theoretical it is a defining factor in how digital ecosystems are understood, analyzed, and remembered. What once appeared to be a neutral layer of internet functionality has evolved into a powerful lens for interpreting structure, behavior, and long-term exposure.
The early underground internet operated on assumptions of disposability. Domains could be replaced, platforms could be rebranded, and identities could shift. But DNS introduced continuity into an environment that relied on fragmentation. Nameservers, historical records, and resolution data created links that persisted beyond the lifespan of any single project.